BEST PRACTICE FOR AN SAP S/4HANA AUTHORIZATION MIGRATION (PART 2 – BROWNFIELD)
In the first part of this blog, I presented the Greenfield approach and showed how you can methodically implement your migration project with the help of the functionalities of the XAMS tools. I also highlighted that a simple transfer of your previous roles to the new SAP S/4HANA Business Suite cannot be done easily, which is why an adjustment of roles is absolutely mandatory. Based on the on-premise product variant, I have presented some project approaches as an example for an initial implementation and, particularly, for a new implementation. In our previous blog post, we discovered the XAMS solutions, which can help with important milestones of your migration project to the S/4HANA cloud user experience:
- the simple role design based on statistical data and easy identification of SAP S/4HANA-related changes
- the efficient execution of the test phase
- the low-risk transfer of operations with the Protected Go-Live
In this second part of the blog, I will walk you through another authorization migration option, the so-called Brownfield migration approach. I will present the procedure, the solutions and the appropriate XAMS features to offer you a comprehensive overview of the possible project approaches and provide relevant examples. Furthermore, you will notice that the two approaches, the Greenfield and the Brownfield, are not that different of a roadmap when it comes to an authorization migration.
Before focusing on the Brownfield approach, I would like to emphasize that, as well as in the first case scenario with the Greenfield approach, almost all business areas of your company are affected by the migration. This is not a simple software update but a consolidation of SAP solutions to move end users to the cloud for a more real-time user experience. We would recommend that you work closely with your business areas during this project to create a sustainable, correct authorization concept of required business processes and achieve a high level of user acceptance of the SAP customers.
The other approach to an authorization migration: Brownfield
With the Brownfield approach, also known as system conversion, you migrate the current SAP ERP 6.0 to the new SAP S/4HANA intelligent enterprise. By doing this, you rely on the existing legacy system and, at the same time, on the old data and old roles. Although this approach leads to completing the SAP S/4HANA migration authorization tasks faster, since the entire system does not have to be restructured, legacy issues are also imported during the system conversion. This makes it difficult to optimize and comply with SAP Best Practices and may prevent you from utilizing the full potential of the authorization features of the SAP HANA database system. When referring to authorizations, SAP S/4HANA-related changes are either adjusted directly in the roles or made available via new roles. If necessary, you can make small enhancements to process flows or your authorization structure. Based on the stability of your processes and the quality of your authorization concept, there are two approaches available, which you can see in figure 1:
- Migration of the SAP authorization concept
- Redesign of the SAP authorization concept
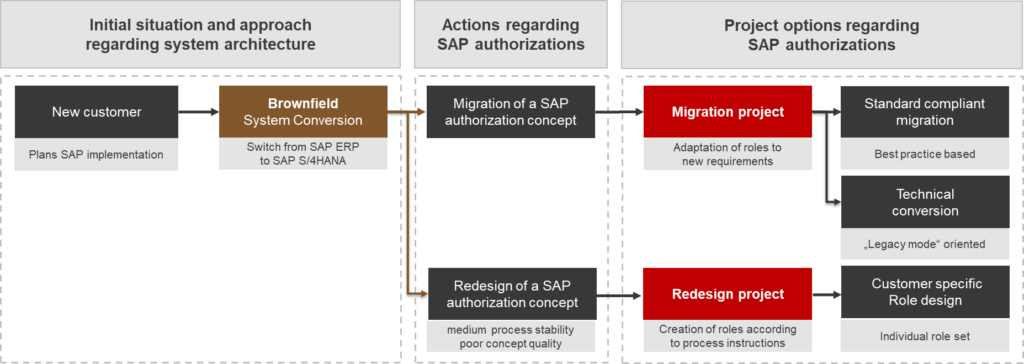
The option of an authorization redesign should be chosen if the SAP ECC authorization concept does not meet security-related requirements, it is difficult to maintain, or processes must be fully optimized. This is ideal for companies that have seen substantial growth through acquisitions, resulting in repeated complexity in the authorizations, and want to adopt the SAP standards for the S/4HANA conversion. If this is not the case and the authorization concept is of good quality, while processes are also stable, the doors are wide open to you for a standard-compliant migration of your SAP authorization concept. But what is a “good authorization concept”?
Quality of authorization concept: The key for a standard-compliant SAP S/4HANA authorization migration
The objective should always be the implementation of a secure and maintainable authorization concept. You can achieve this by creating standardized and simplified job roles, while also taking into consideration security-related requirements, both internal and external. A high-quality concept or role design does not only fulfill security factors such as avoiding segregation of duties conflicts or critical authorization issues that can be identified with a GRC tool, but it also requires an SAP standard-compliant role authorization design with strict use of the authorization object and field default values (keyword transaction SU24). In the case of proper role maintenance, no changed or manually added authorization objects are used during the migration and maintenance of roles, with exceptions such as generated SAP_ALL profiles. In particular, role profiles with manual start objects (S_TCODE, S_SERVICE, S_START and S_RFC) cannot be merged in the profile generator with the default values stored in SU24 and transferred to SAP S/4HANA.
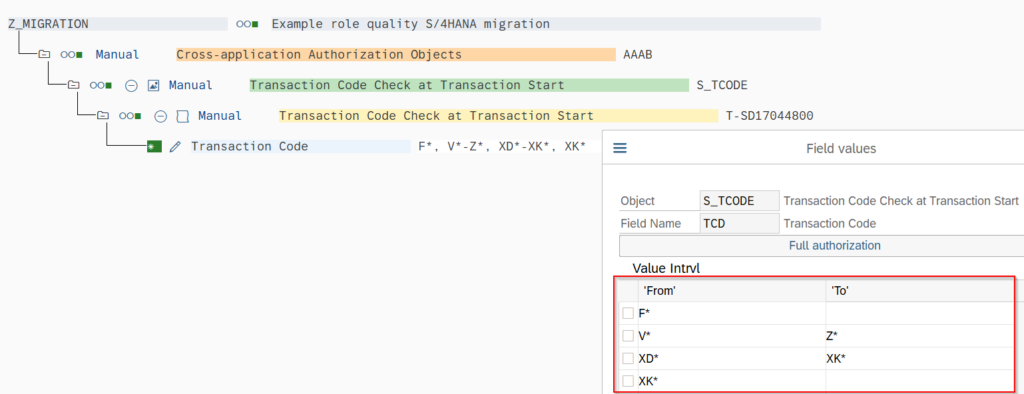
Roles with value ranges in the start objects mentioned before are also excluded from a standard-compliant migration, since the comparison of the role menu objects with the Simplification List for SAP S/4HANA is difficult or even impossible to identify proper mapping without manual intervention. See Figure 2.
For a standard-compliant migration, the SAP best practices are the top priority as the SAP S/4HANA-relevant adjustments occur directly in the old roles.
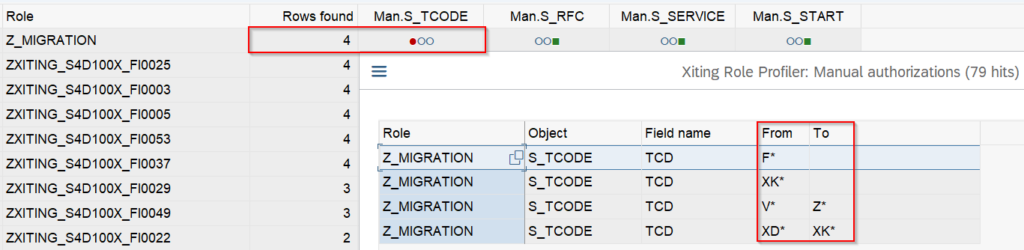
Finally, checking the technical quality of roles is a crucial factor before choosing the suitable business case migration approach for your SAP ERP system landscape. To simplify the process of analyzing the quality of roles, the Xiting Role Profiler module of the XAMS tools provide reports that help you identify the manual authorizations. In doing so, the analysis enables you to scan the technical deficiencies of actively assigned roles and evaluate the roles individually. This analysis shows you whether it is technically and efficiently possible to remedy the technical deficiencies and, depending on these results, whether a standard-compliant SAP S/4HANA migration can be performed or not. The following figure shows the analysis of roles in the Xiting Role Profiler:
BROWNFIELD PROJECT OPTION 1: Technical conversion – a compromise
The technical conversion is a compromise solution for companies that do not have a standard-compliant role concept and cannot carry out a holistic redesign of the authorization roles due to time constraints and possible downtime. However, a redesign of your entire authorization concept ultimately must be considered eventually in order to be able to guarantee the maintainability and security of the roles in the future. Since the existing role concept was not implemented in an SU24-compliant manner, a profile comparison has a correspondingly negative impact on the existing characteristics and, therefore, contains high risks. During the technical conversion, necessary S/4HANA applications must be provided via additional new roles and the old roles must be retained. This procedure may involve even greater effort in your digital transformation.
BROWNFIELD PROJECT OPTION 2: Standard-compliant SAP S/4HANA authorization migration – best practices
Entirely in accordance with Xiting Best Practices, I will show the procedure for a standard-compliant SAP S/4HANA migration and go into the XAMS features that can be a welcome help in handling the complex work packages. Figure 4 shows the three main project phases. If you compare both migration approaches, Greenfield and Brownfield, you will find that they differ from each other in only one phase, namely the role design phase. The test simulation and the protected go-live are carried out in a similar manner. These two phases have already been explained in the first part of the blog and are, therefore, not described in detail here.
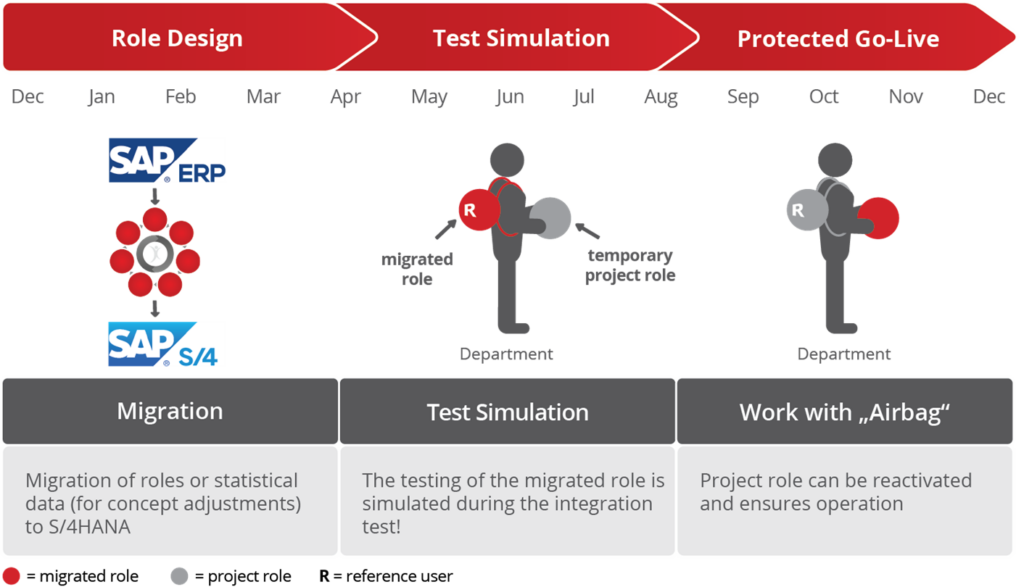
Phase 1 of the standards-compliant SAP S/4HANA authorizations migration: role design/migration
In this project step, all SAP S/4HANA-related changes in your roles are analyzed and finally migrated based on the “Simplification List for SAP S/4HANA”, from SAP, which is also integrated in the XAMS and delivered to you on a release base. This saves you the time-consuming task of manually comparing your role content with the simplification list.
For example, with the XAMS Role Profiler roles assigned to users are checked for invalid transactions in SAP S/4HANA. You will receive a results list with roles that need to be adjusted if you want to use them after the system migration to SAP S/4HANA.

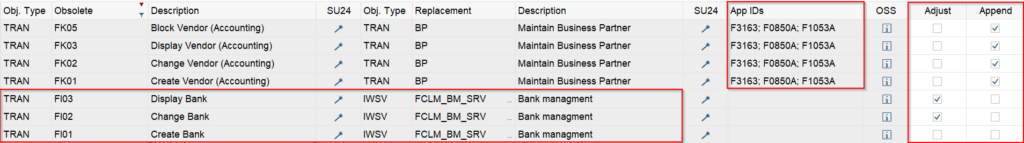
Another attractive feature of this report is the listing of new replacement objects, e.g., transactions, SAP Fiori apps or other web applications. As can be seen in the following figure, you will receive comprehensive information that is also crucial for your business areas.

In Figure 7 you can see obsolete transactions, e.g., “XK01” (Create customer), which is replaced by the transaction “BP” (Edit business partner), or, if necessary, by the Fiori applications F3163. In the “Customize” column, you can replace the obsolete applications ad hoc in your roles or enlarge them using the check box in the “Add” column. Finally, the role menu in PFCG is adjusted and the authorization profile of the role can be further processed in the profile generator.
Note:
OData services that are listed as replacements indicating that user interface SAP Fiori applications are required.
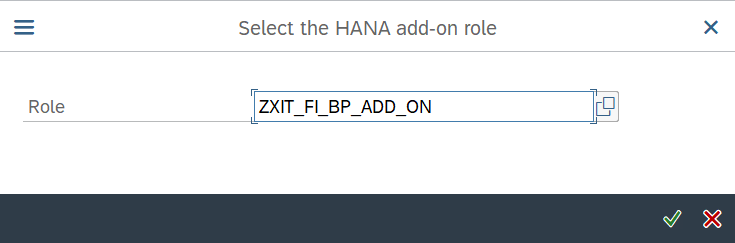
As mentioned at the beginning, you can also react flexibly to small process enhancements with the Brownfield approach, for example by creating additional roles. Let’s take as an example the need for a restrictive assignment of the transaction “BP” (process business partner). With the XAMS Role Profiler you get an extension function in which you can add SAP S/4HANA criteria directly to a new role:
In summary, the following can be stated: With the XAMS you receive important tools for all work steps of this migration phase, while taking into account the correct procedure, in order to migrate your roles conveniently and sustainably in accordance with the standard.
Side note – in-house developments: The restructuring of the data model that took place in SAP S/4HANA could have side effects on your in-house developments. Customer programs should therefore be checked for further usability and, if necessary, adjusted in the source code, e.g., if programs access outdated tables in SAP S/4HANA.
Conclusion: Greenfield or Brownfield?
Now you know the project options of the Greenfield and the Brownfield authorization migration approaches by using the XAMS. There is no general recommendation when choosing the right approach. This decision-making requires the evaluation of many customer-specific factors and ultimately depends on your preferences and resources. A comprehensive system analysis performed by Xiting, including an S/4HANA readiness check or sharing knowledge on this topic with one of our experienced consultants as part of a SAP S/4HANA workshop can help you make the right choice. The XAMS offers practical solutions for both approaches.
In addition, Xiting offers a comprehensive range of services on all topics related to SAP security, SAP S/4HANA and SAP authorizations. You can also attend our regular webinars focused on different topics around SAP Security. Feel free to contact us and ask one of our experts about the Brownfield and the Greenfield approaches and about the best practices when migrating your authorizations to SAP S/4HANA.
- Success Story: Zumtobel Group (Extended Version) - 7. September 2023
- BEST PRACTICE FOR AN SAP S/4HANA AUTHORIZATION MIGRATION (PART 2 – BROWNFIELD) - 19. September 2022