The TOP 20 SAP IT base tables with special protection requirements in SAP S/4HANA
IT Basis Tables in SAP S/4HANA SAP S/4HANA is a comprehensive business suite used by many companies worldwide. The software enables businesses to automate and streamline processes such as finance and accounting, procurement and sales as well as human resource management, linking and optimizing these processes. As a result, large amounts of data accumulate in the complex and data-intensive world of SAP S/4HANA and SAP Fiori. SAP Basis tables serve as the foundation for smooth business processes in this environment. As the core of system administration, they include essential system requirements and data, as well as sensitive and business-critical information. However, some of these basic tables are particularly critical for the IT security of the system. This data is crucial for the system’s operability and, therefore, requires special protection.
In this blog, we will take a closer look at the “TOP 20 SAP Basis Tables with Special Security Needs” to understand why protecting this data is of the utmost importance and how companies can ensure the integrity and confidentiality of their information through appropriate security measures. Join me in exploring the world of these significant tables and the challenges associated with securing them. First, I will address the concept of the security needs of SAP Basis tables, and then I will also highlight 20 specific critical tables in this environment and their importance for IT security in SAP S/4HANA. During this analysis, I will also present ways to enhance the security of these tables and monitor them continuously.
In a SAP S/4HANA Core System with an underlying SAP HANA database alone, there are thousands of different tables, with the number increasing exponentially with each additional module and add-on. Therefore, the following SAP Basis tables primarily focus on the IT component BC, as they are important components of a running and operational SAP S/4 HANA system. The mentioned critical basic tables are, however, only a part of the SAP IT Basis tables present in SAP S/4HANA. For simplicity, they will be referred to as SAP Basis tables in the following information. Additionally, you can apply most of the information below analogously to SAP ERP (ECC) as well.
The Five Most Important Reasons for the Special Protection Needs of Tables iN SAP S/4HANA
Tables in SAP S/4HANA often have special protection needs because they contain sensitive, system-specific and business-critical data. This data can include information about finances, personnel, customers, suppliers, production plans, intellectual property and other business processes. Often overlooked is the fact that SAP Basis tables, in particular, form the cornerstone of the entire SAP S/4HANA system. They contain, for example, the necessary customizing, master data, transactional data, and thus provide the technical foundation for a running and upgradable ERP system. This results in a special protection need to safeguard all this data from unauthorized access, manipulation, loss or damage. There are five important general reasons why tables in SAP S/4HANA need protection:
Data Privacy and Compliance
Many of the information stored in the tables are subject to data protection regulations and legal requirements. Companies must ensure that they protect this data appropriately and provide access only to authorized users.
Data Integrity
Tables often store data that is essential for the proper operation of the company. Unintentional or malicious alterations to this data could lead to malfunctions and operational disruptions.
Access Controls
By implementing protective measures, companies can ensure that only authorized employees can access specific tables. This helps minimize security vulnerabilities and prevent unauthorized access.
Risk Management
Companies need to assess security risks and take appropriate security measures to minimize potential threats to their data. A customized risk management framework also plays a pivotal role in this process.
Trade Secrets
Some tables contain proprietary information that is strategically important for the company. Protecting these trade secrets is crucial to maintain competitive advantages and prevent potential economic harm.
Please always keep in mind that it is the responsibility of every company to configure and manage these security features appropriately to ensure the integrity, confidentiality, and availability of their data.
To meet these security needs, SAP S/4HANA provides various security mechanisms such as proper authorization management based on the ‘Need-to-Know’ principle and active table logging with its monitoring. The latter requires active logging in transaction SE13 and correct configuration via RSAU_CONFIG. Starting from SAP NetWeaver 7.50, there are new transactions for the Security Audit Log (SAL) (SAP Note 2191612). Configuration of the Security Audit Log is now done using transaction RSAU_CONFIG instead of transaction SM19. However, you can still navigate from transaction SM19 to RSAU_CONFIG_MAINT or RSAU_CONFIG_SHOW. For more information on SAL, please feel free to check out the blog on this topic by my colleague Adam Egeric.
Access Scenarios for SAP Tables
Before we dive into the details of critical tables in SAP S/4HANA, I’d like to briefly mention a few words about access scenarios. In the SAP standard, there are a total of four ways to access tables. You must consider and restrict all of the following access scenarios at a minimum to prevent unwanted or potentially harmful access to critical SAP tables.
Access through SAP GUI Business Transactions or SAP Fiori Apps
Depending on the job functions of individual end-users, they may interact with and modify different tables in the SAP system as part of their daily work. For example, a financial accountant using transactions like FB01, FS00, FD01, or FK01 may also access and potentially modify data in the central FI/CO table ADCOCA. The same principle applies to the corresponding SAP Fiori apps. Therefore, it is crucial to restrict access through authorization profiles based on the ‘need-to-know’ principle when defining job roles to protect data in accordance with guidelines. Otherwise, there is a risk that users, intentionally or unintentionally, may arbitrarily change records related to creditors, debtors or their fixed associations with corresponding business areas or cost types.

Access via Administration Transactions
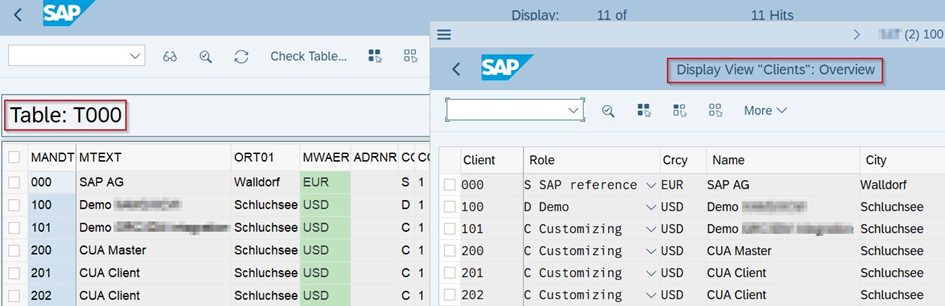
Basis administrators in particular have extensive and critical permissions in the SAP system because, as part of their job roles, they are responsible for maintaining and managing the entire system. For example, it’s not only direct access to table T000 that is critical, but also the associated administration transaction SCC4, through which one can then maintain table T000.
Access via Basis Transactions for Table Access
Direct access to tables for viewing or making changes is facilitated in the SAP standard through transactions such as SE16, SE16N, SE16N_EMERGENCY, SE16H, S416N, S4H16N or SM30. These generic accesses are highly critical, and their assignment to job function roles should be strictly avoided in productive systems. Instead, consider using parameter transactions, which allow you to jump directly to the intended table without, with the right settings, getting the initial selection screen for all tables.
Access via Debugger
Another critical form of access, if not the most critical, to any data in an SAP system is through debugging permissions, which are enabled through the authorization object S_DEVELOP. Therefore, it is crucial to ensure that these permissions are only granted on a productive system using an emergency user concept, or at most, as display-only rights on a limited basis. Otherwise, it is possible to bypass all access controls in an SAP system and gain access to view and modify all data.

The 20 Most Critical Base Tables and Their Contents in SAP S/4HANA
Tables in SAP S/4HANA are the fundamental data storage structures. They contain data required for various business processes, such as customer and vendor master data, financial accounting data, material master data, and many more. There is a wide range of SAP base tables in SAP S/4HANA, all contributing to support the IT side of business processes. Below is a selection of critical SAP base table names:
Alphabetically sorted
1. AGR_1251 – Authorization Data in Roles
The table AGR_1251 is a customizing table that contains information about the usage of authorization objects and their associated values in roles. This table is part of the authorization concept in SAP and is used to link specific actions or business processes to specific authorizations based on the underlying roles. As a result, it contains sensitive data regarding access rights and is therefore highly critical in terms of data protection policies, preventing unauthorized access and avoiding disruptions to business processes.
2. AGR_USERS – Role-User Assignment
This table contains information about the assignments of roles to users in the system. It provides details about the permissions and access rights granted to users with these role profiles. It is essential to tightly control access to the AGR_USERS table and the management of authorization roles in an SAP system to ensure that only authorized users receive the appropriate access rights. Careful authorization assignment is crucial to ensuring the security of the SAP system and preventing unauthorized access to sensitive data or functions.
3. CDHDR and CDPOS – Change Logs
The SAP tables CDHDR (Change Document Header) and CDPOS (Change Document Items) are part of the change document system in SAP and contain information about changes made to specific objects within the SAP system. These tables are used for change management to enable tracking and documentation of changes to critical data or configurations. They are therefore crucial for monitoring changes to critical data and supporting compliance requirements and traceability.
4. DD02L – Table Definitions
In SAP, the table DD02L contains crucial information about data objects defined in the Data Dictionary of the SAP system. The Data Dictionary is a central component that enables the definition and management of data structures and elements stored in the database. Therefore, this table is critical. Changes or manipulations to the data objects in the Data Dictionary could lead to serious issues in the SAP system, such as data inconsistencies, unexpected errors, or even data loss.
5. E070 and E071 – Change Information in Transport Management
The SAP tables E070 (Information about transport requests and transport numbers) and E071 (Change documents of repository objects in transports) are also both part of the change document system in SAP and serve the management of changes to transport requests. They provide insights into the development process, change history and transports of development objects between different systems. Therefore, these tables are critical as they contain important information about changes to critical objects in the SAP system and are meant to ensure the integrity of the development and change process.
6. JEST and JCDS – Status and Change Tracking
The tables JEST (Change Documents – Object Status) and JCDS (Change Documents – System and User Status) are both part of change management in SAP and contain information about the status of objects in various processes and change documents. These two tables hold critical information about the status of objects in the SAP system and the change history of these statuses, making them closely related to change management, the development process and object lifecycle management. Access to these tables should therefore be restricted to authorized users with the appropriate permissions to ensure the integrity of status information and change documentation.
7. RFCDES – Table for Remote Function Call Destinations
The RFC destination data is primarily stored in the RFCDES (and RFCDESCTRL) table. This table contains entries for individual RFC destinations defined in the system. Each entry includes information such as the name of the RFC destination, the type of connection (e.g., TCP/IP or HTTP), the target host’s address, port and other relevant connection details. The RFCDES table is critical as it contains sensitive information about connections to other systems. Unauthorized access to this information can lead to security vulnerabilities and jeopardize the SAP system and associated systems. It is important to restrict access to this table and ensure that only authorized users with the appropriate permissions have access to RFC destinations and their connection information.
8. T000 and T000T – System and Client Information
This base table contains general settings and configuration data for the entire system. This includes settings for language, date and time and currency. Changes to these settings can have far-reaching impacts on the system and should, therefore, be made with caution.
9. TBTCO – Job Status Overview Table
The table TBTCO contains information about the statuses and details of batch jobs in the SAP system. TBTCO serves as an overview of the various batch jobs in the system, allowing for their management and monitoring. Since batch jobs typically control important system processes and run automatically without user interaction, it is crucial to protect access to the TBTCO table. Unauthorized access or unauthorized changes could lead to disruptions in job execution and, in the worst case, operational disturbances in the SAP system.
10. TFDIR – Function Modules
This table contains essential information about function modules in the SAP system. Function modules are predefined ABAP functions that perform specific tasks and can be reused in other ABAP programs. They serve to provide specific functionalities that can be called by other parts of the program. Inadequate management of this table can lead to security risks and compliance violations. For example, users could have unauthorized access to certain function groups. It is important to carefully monitor access to this table and the use of function groups to prevent security vulnerabilities, maintain the integrity of functions and protect business processes.
11. TADIR – Repository Object Catalog
This table contains information about all ABAP repository objects in an SAP system, such as ABAP programs, function groups, transactions, database tables or data elements. Therefore, the TADIR table is more comprehensive and general than the TRDIR table. Inadequate management of this table can lead to security risks and compliance violations. For example, users could have unauthorized access to specific repository objects and corrupt them with extensive permissions. Sufficient protection must be explicitly maintained here, as it is one of the most critical tables in an SAP system.
12. TRDIR – Program Directory
It contains information about ABAP repository objects in an SAP system. In contrast to the TADIR table, the TRDIR table provides specific information about ABAP repository objects encapsulated as transactions. It lists the transaction codes (TCODEs) in the SAP system and associates them with the underlying programs or functions called when executing these transactions. It is essential to carefully monitor access to this table and restrict access to a selected group of individuals to maintain data security.
13. TSP01 – Spool Requests
The SAP table TSP01 contains information about permissions for managing spool requests in the SAP system. Spool requests are output requests generated during the processing of reports, print jobs or other SAP processes and are temporarily stored in a queue (spool) before being printed or exported into other formats. The TSP01 table is critical as it houses sensitive information about permissions for managing spool requests and their contents.
14. TSTC – Transaction Basics Table
This base table contains data about transaction codes used in the system. Transaction codes are shortcuts for specific business process applications or functions, allowing users to quickly access specific functionalities. Changes to these transaction codes can impact user-friendliness and business processes. The TSTC table is, therefore, crucial for controlling access to transactions and preventing unauthorized access.
15. USR02 – User Data
The SAP table USR02 (User Data) contains essential information about user accounts in the SAP system. This table stores user data, including usernames, encrypted passwords, validity dates, lock dates and other information related to user accounts. In the context of data privacy and general IT security, access to the USR02 table must be protected, and measures should be taken to ensure that only authorized users with the appropriate permissions have access to user accounts and data.
16. USR40 – Unauthorized Passwords
This table contains a list of passwords that are not allowed for security reasons. When users want to set a new password or change their password, the SAP system checks if the entered password is included in this table. If the password is listed in the “USR40” table, it is considered insecure and the system rejects the password change request. Users are then prompted to choose a different, more secure password. Only a selected group of individuals should have access to this table, as altering the table could quickly grant access to the SAP system or make passwords too easily discoverable through brute force attacks.
Analyzing critical access rights to tables using the Xiting Authorizations Management Suite
In summary, careful management of user data, role profiles and change logs can help ensure that only authorized users can access critical data and make changes. Restricting access to tables is not only done through S_TABU* authorization objects but also through administration transactions and basis as well as debug-replace authorizations. To analyze this comprehensively, you need both an analysis tool and a rule set, which Xiting provides with their all-in-one solution, XAMS.
Xiting’s Critical Risk Authorization Framework (CRAF) is a valuable tool in the realm of IT security, especially for SAP system landscapes. This unique rule set consists of numerous rules and best practices developed, based on industry standards, regulatory requirements, years of developer expertise and collaboration with auditing partners. It enables continuous risk assessment of system activities and processes, based on underlying authorizations. This helps identify potential risks and vulnerabilities in the system, allowing measures to be taken to minimize or eliminate these risks.
Through the use of CRAF, you can ensure that your SAP systems always meet current security requirements, minimizing the risk of security breaches and data misuse. A rule set like CRAF is a crucial component of a holistic IT security strategy and should be taken seriously by organizations to ensure the security and integrity of their systems and data.
The complexity and versatility of Xiting’s CRAF will be demonstrated with practical examples in an upcoming blog post titled “Xiting’s CRAF Rule Set – Putting an End to Critical Authorizations and SoD Violations.”
Conclusion
The above-mentioned critical SAP base tables are of paramount importance for IT security in SAP S/4HANA and its SAP applications. By monitoring these tables, companies can ensure that their data and processes are protected from unauthorized access and manipulation. Don’t forget that managing critical tables is an essential part of IT security in SAP S/4HANA for any company, whether it’s on-premises or cloud-based. It’s important for companies to identify their specific list of critical tables and manage and protect them accordingly.
Implementing a comprehensive security strategy that includes monitoring and managing tables to ensure the security of data and processes is crucial. Poor management of these tables can lead to serious security issues, such as unauthorized access to sensitive data or changes to data without the appropriate approval process or change logs.
Therefore, it is crucial for companies to be aware of the importance of these tables and take appropriate measures to strengthen their IT security and minimize the risk of security breaches. Compared to SAP’s standard analysis tools, XAMS offers much more extensive and comprehensive features to facilitate targeted and clear security monitoring. You can benefit from features like alert functions, creating a customized rule set based on existing best practice rules or system-wide monitoring. We even offer various rule sets and content, such as critical base authorizations, SAP HR or GDPR rule sets.
Furthermore, XAMS offers numerous other innovative features for your authorization management needs. Feel free to join one of our weekly webinars to get a closer look at our suite. Additionally, we provide a variety of different services and products to assist you in maintaining your authorization system.
- The TOP 20 SAP IT base tables with special protection requirements in SAP S/4HANA - 7. September 2023
- Migration to SAP S/4HANA – Basics (Part I) - 30. September 2022